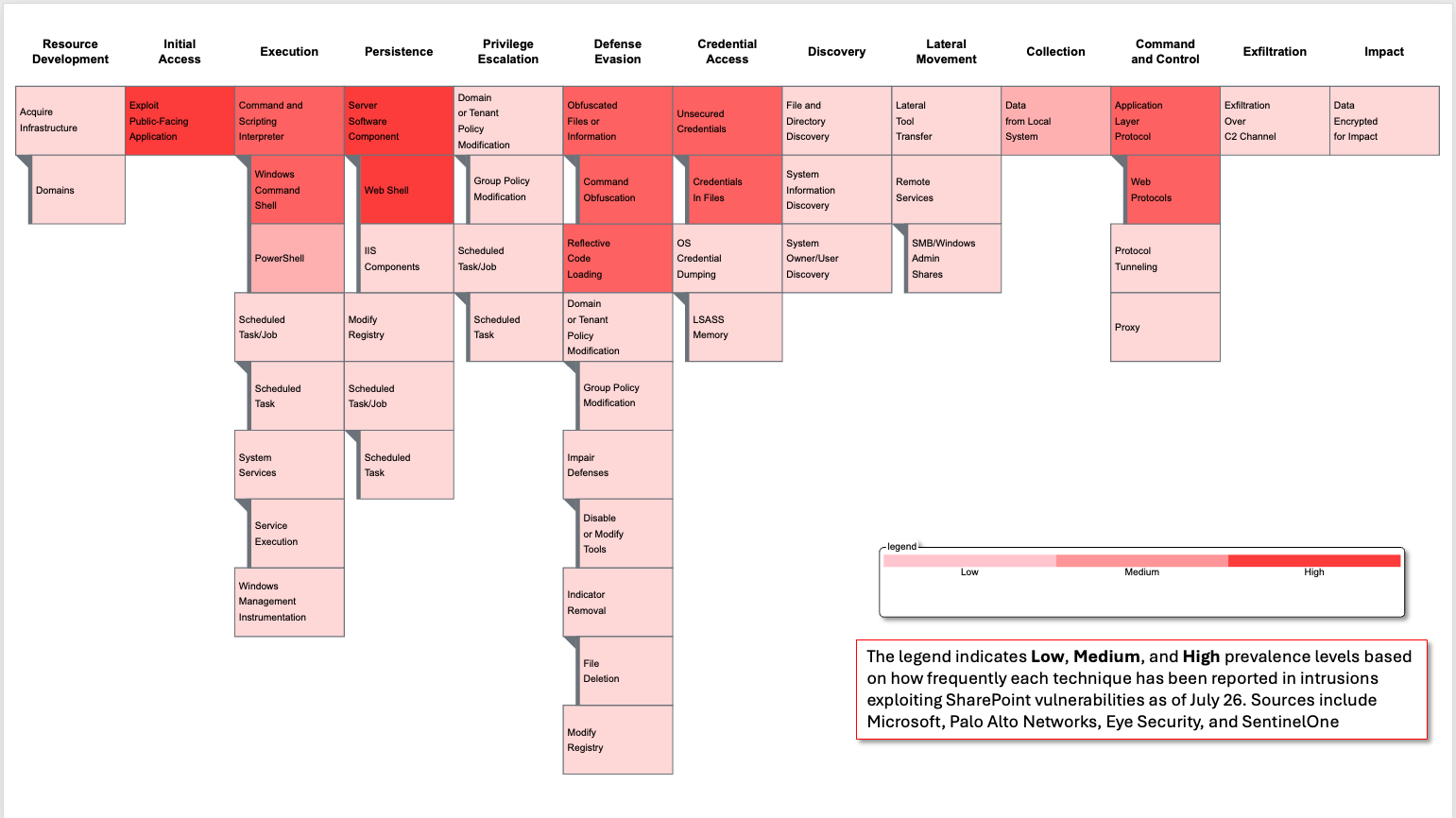
MITRE ATLAS Grows through Collaboration with CTID and Industry
Secure AI expanded MITRE ATLAS™ with new techniques, mitigations, case studies, a Technique Maturity filter, and rapid-response and emulation capabilities to strengthen defense of AI-enabled systems.