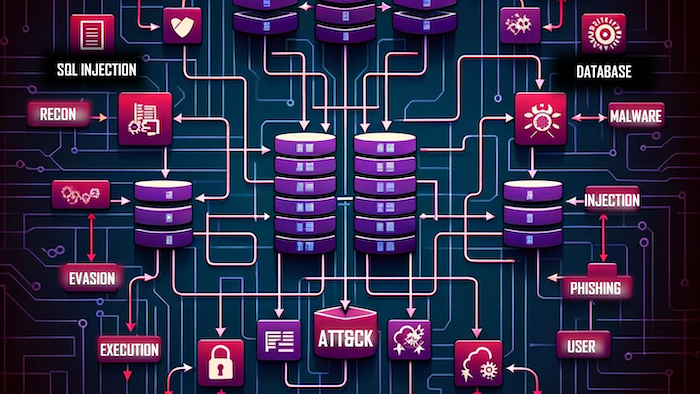
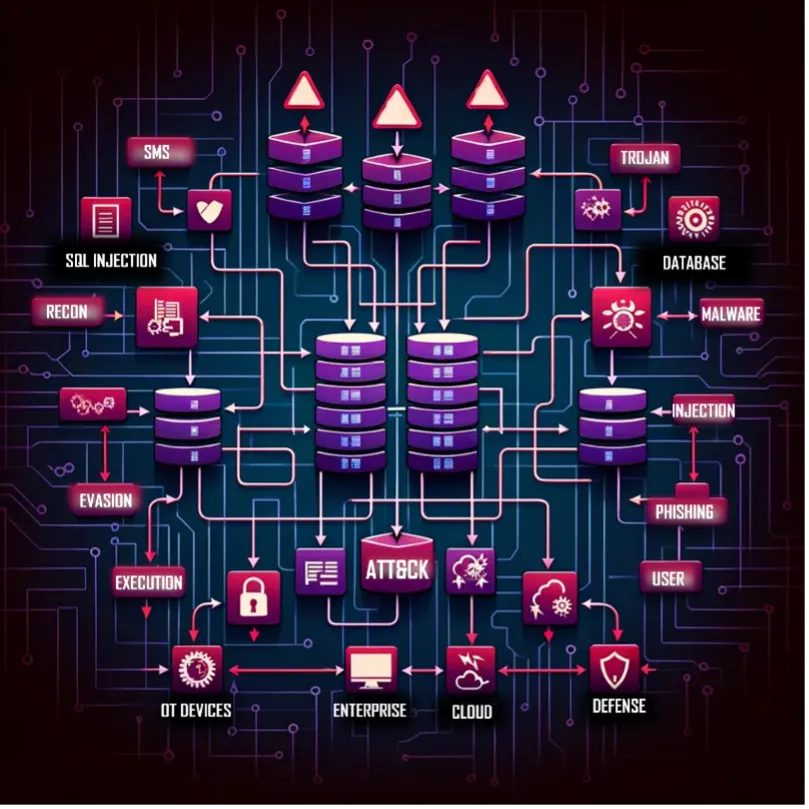
INFORM Your Defense
MITRE INFORM is a program-level assessment designed to show how threat-informed your organization is and where to improve next across cyber threat intelligence, defensive measures, and test and evaluation. Turn insight into action and see your threat-informed posture at a glance and know exactly …