Fraud Fighters United with MITRE F3
MITRE Fight Fraud Framework (F3) is a behavior-based model of fraud actor tactics and techniques that gives fraud and cyber defenders a shared …
By Mike Cunningham, Suneel Sundar and Tiffany Bergeron • April 9, 2026
Fraud actors do not operate within the boundaries of organizational charts. They move seamlessly across cyber systems and fraud channels, combining techniques to steal your money and the bank’s money. Fraud analysts see part of the activity and react. Cyber defenders see another and engage in proactive defense. If defenders remain separate, organizations struggle to connect signals, understand incidents, and prioritize defenses. That gap slows response, precludes prevention, and drives ever-increasing losses.
MITRE Fight Fraud Framework™ (F3) changes that.
MITRE F3™ is a behavior-based model of fraud actor tactics and techniques, developed by cyber and fraud analysts together and derived from real-world fraud incidents. It gives fraud and cyber defense a common structure to describe what happened, relate events, and disrupt fraud outcomes through their combined strengths.
Developed in collaboration with CTID members including A-ISAC, Citigroup, CrowdStrike, FS-ISAC, JPMorganChase, Lloyds Banking Group, Marsh, National Retail Federation, RH-ISAC, Standard Chartered, and Verizon Business, F3 reflects how fraud occurs, not how organizations are structured.
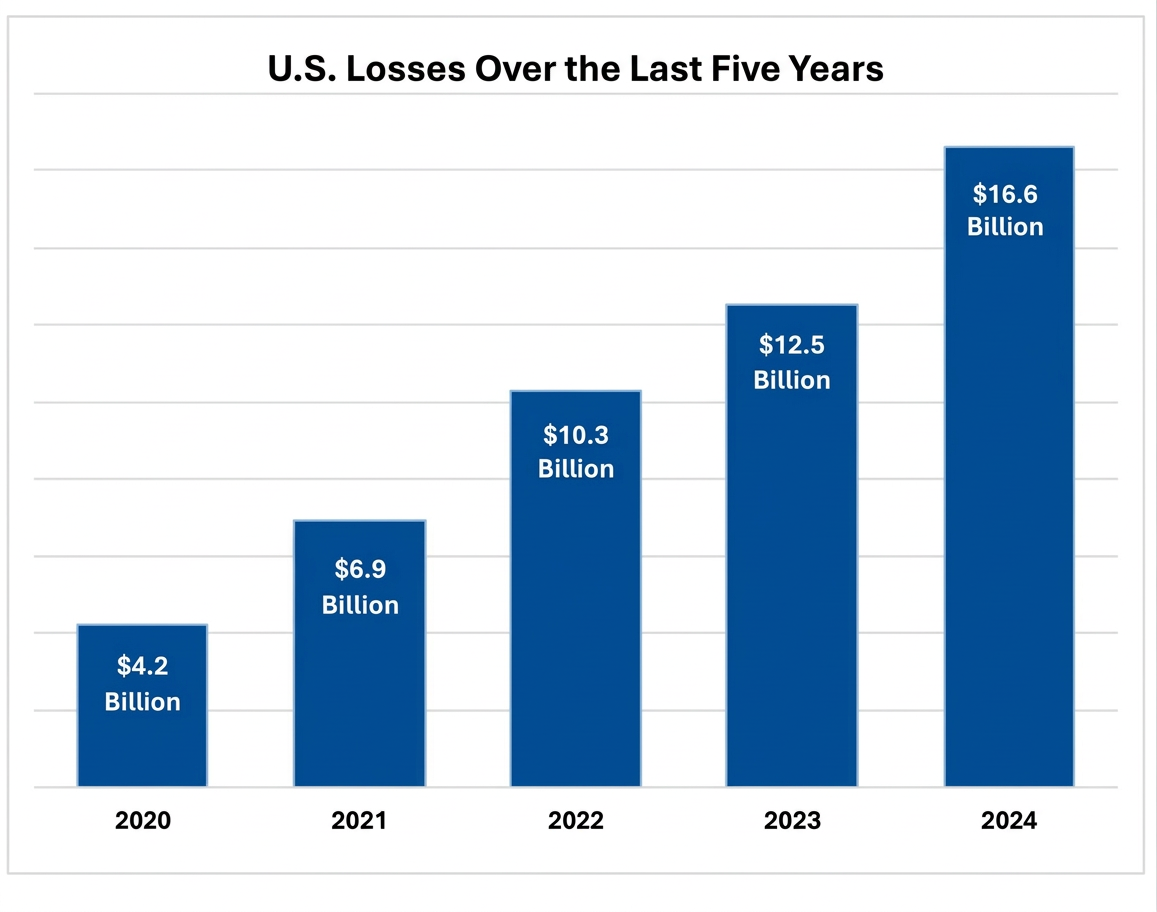
Financial fraud hurts us all. The U.S. Federal Bureau of Investigation reports over $50 billion in losses from more than 800,000 complaints across 2020 to 2024. And the quantity of loss increases year-over-year. Worldwide, this multiplies to $580 billion lost to fraud scams and bank fraud schemes in 2025 alone.
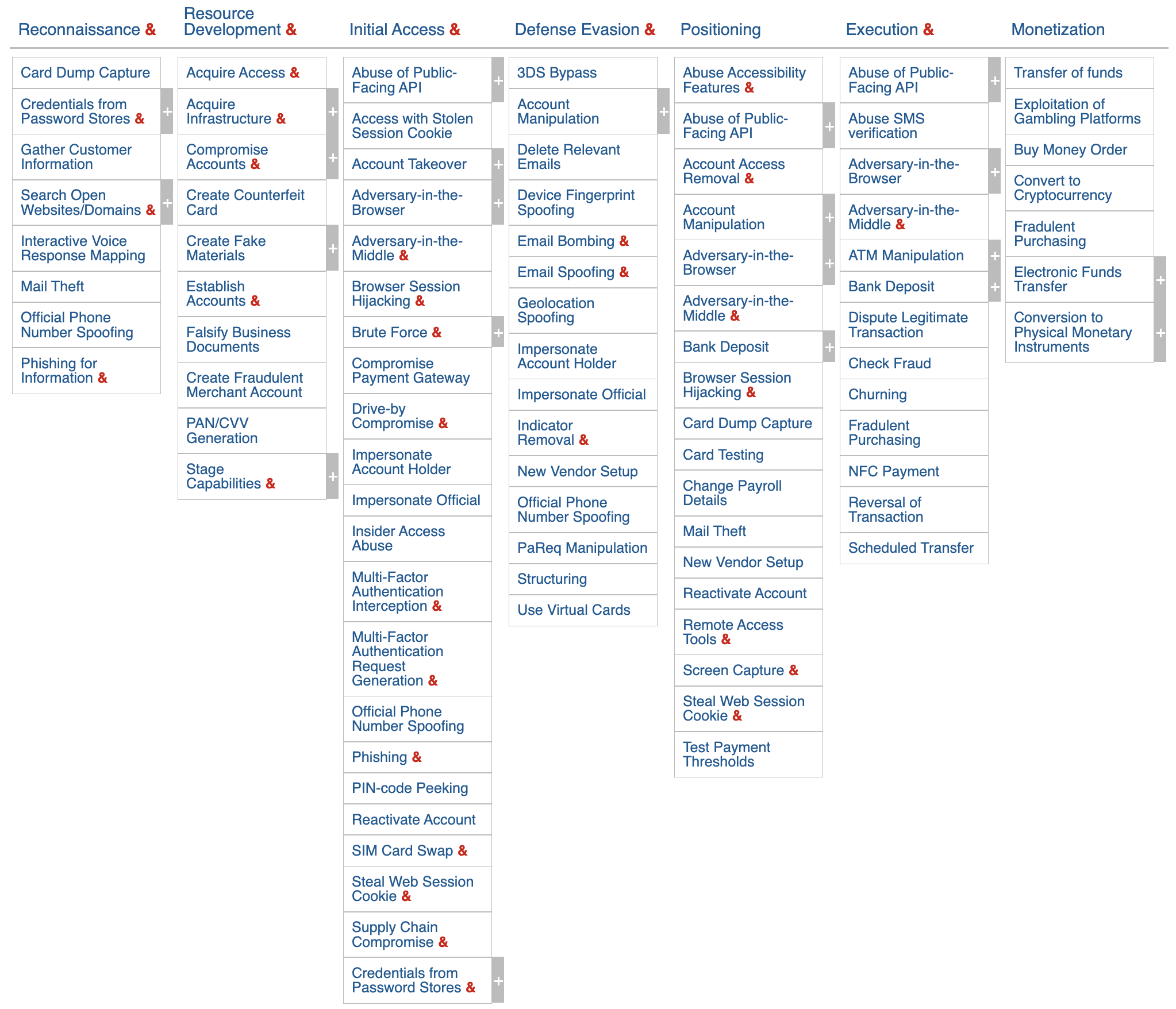
Like MITRE ATT&CK®, F3 organizes fraudster behavior into Tactics - the why of the fraudster - and techniques - the how. However, fraud introduces behaviors that are absent in ATT&CK, such as how adversaries prepare accounts, manipulate transactions, and extract value. F3 addresses this gap by introducing two fraud-specific tactics:
These additions capture the uniqueness of fraud where success depends on moving and extracting value, not just gaining access. By capturing those stages, F3 allows defenders to trace fraud activity from initial compromise through financial impact.
Where a tactic or technique already exists in ATT&CK, F3 uses those directly. Most F3 tactics will be familiar to threat-informed defenders, though F3 modifies their definitions to the specific fraud outcomes:
This structure creates a shared language that allows cyber and fraud defenders to enumerate the material events in a fraud incident, connect cyber activity to financial outcomes, and align detection, prevention, & response strategies.
Where F3 introduces unique techniques, we extend ATT&CK’s model with F1XXX-series techniques that capture fraud-specific actions while remaining compatible with the ATT&CK schema.
Our guiding light for F3 was simple: accurately represent how fraud actors operate, in a way that helps institutions defend against them. To do that, we adopted design principles modeled on MITRE ATT&CK and tuned them for financial fraud:
These principles keep F3 tightly aligned to fraud behavior and ensure that the framework remains usable for categorizing, detecting, and preventing fraud incidents.
Fraudsters have evolved from smash-and-grab check washers to scammers with spoofed credentials, social engineering savvy, and software manipulation. Fraud prevention requires coordination across teams that traditionally operate in silos. F3 is the universal translator that enables that coordination.
With F3:
This shared foundation enables organizations to move from fragmented visibility to coordinated, threat-informed defense against fraud.
Fraudsters are not slowing down. New schemes will emerge, and adversaries will adapt their techniques. F3 is designed to keep pace with new techniques so that threat-informed fraud defenders can stay ahead.
The framework is a living knowledge base, continuously updated with new techniques, refinements, and community input. It reflects real-world observations and grows alongside the fraud-fusion community. As we grow F3, we will include more resources for threat-informed fraud defenders such as data sources to detect fraudster techniques and recommended mitigations to counteract them.
You can explore the framework, suggest edits to techniques, and contribute improvements on the F3 website.
F3 improves through community use and contribution. There are several ways to get involved:
We welcome your input to help refine F3 and strengthen its value to the fraud and cybersecurity communities. Submit feedback or contact us directly for collaboration opportunities.
© 2026 The MITRE Corporation. Approved for Public Release. ALL RIGHTS RESERVED. Document number
PR_25-02691-6.
MITRE Fight Fraud Framework (F3) is a behavior-based model of fraud actor tactics and techniques that gives fraud and cyber defenders a shared …
MITRE CTID’s latest ambiguous techniques research turns context into confidence with minimum telemetry requirements and a confidence scoring …
Threat-informed defense changes the game on the adversary. Threat-informed defenders read their adversaries’ playbooks and then orchestrate a …