Secure AI
A collaboration with MITRE ATLAS™ to advance security for AI–enabled systems that takes a threat-informed approach, enables rapid exchange of new …
February 23, 2022
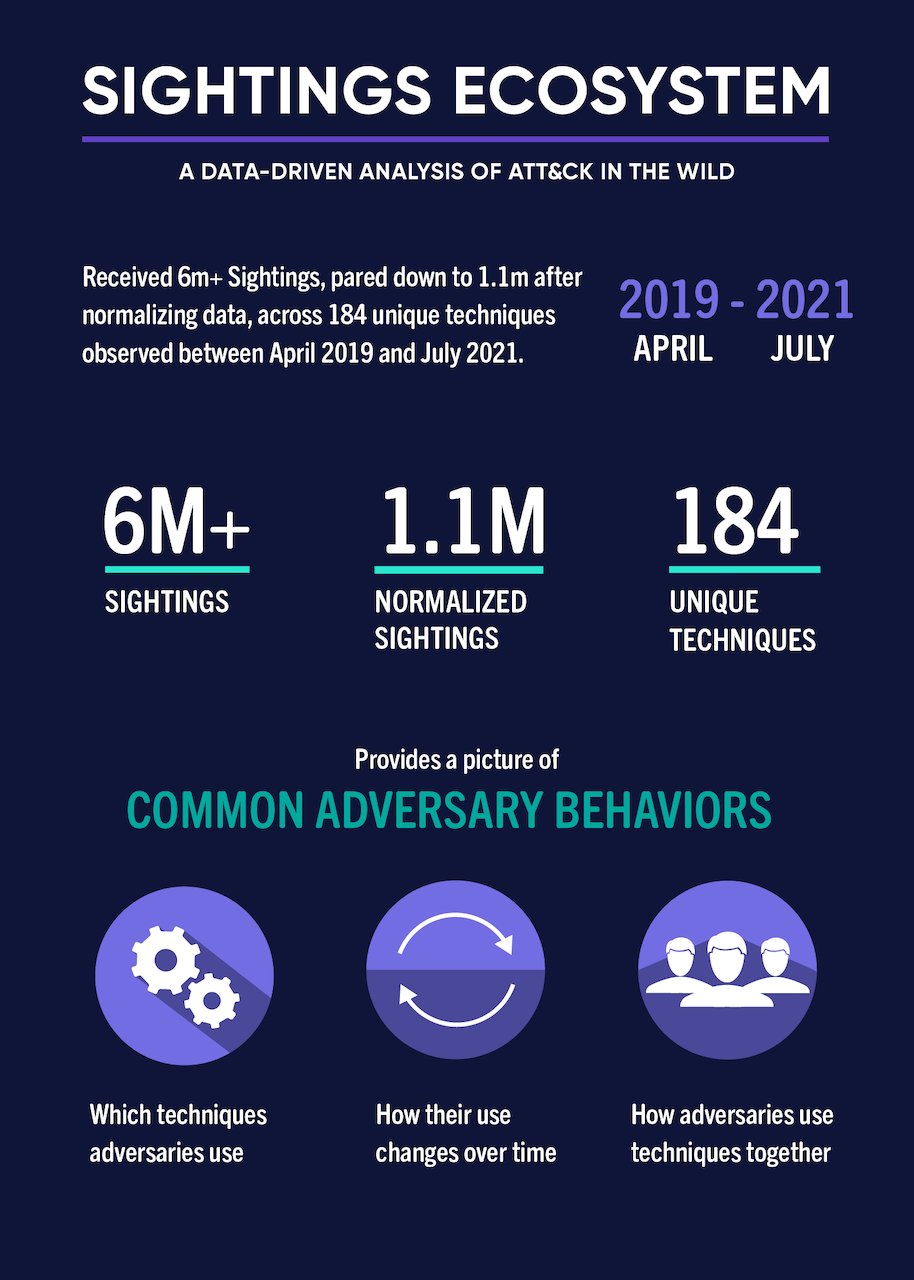
This project provides cybersecurity defenders and researchers with critical insight into real-world, in the wild adversary behaviors mapped to ATT&CK. The ecosystem aims to fundamentally advance the collective ability to see threat activity across organizational, platform, vendor and geographical boundaries. Voluntarily contributed raw “sightings”, or observations, of specific adversary TTPs are mapped to ATT&CK, anonymized, and aggregated to produce intelligence describing insights from that data.
This is an old version of the Sightings Ecosystem project. For the latest version, see: Sightings Ecosystem.
Defenders lack visibility into which adversary behaviors they should focus their attention on first.
Build and operate a way for organizations to safely contribute sightings of specific ATT&CK TTPs powering analytics that give defenders a picture of what TTPs are used where and when.
The sightings ecosystem injects real-world data and insights from that data into the decision-making process of defenders, allowing them to focus their resources on the highest priority problems.





A collaboration with MITRE ATLAS™ to advance security for AI–enabled systems that takes a threat-informed approach, enables rapid exchange of new …
The Fight Fraud Framework strengthens fraud analysis by giving teams a clear behavioral structure to identify risks, focus investigations, and …
With Ambiguous Techniques, you will reduce false positives, focus on the highest‑value log sources, and uncover adversarial use of …
Sign up for our "Stay Informed" mailing list to receive announcements for project publications, upcoming events, and other news about the Center.