September 10, 2020
A Set of Common Emulation Plans
The Adversary Emulation Library includes a collection of adversary emulation plans that allow organizations to evaluate their defensive capabilities against the real-world threats they face. Emulation plans are an essential component in testing current defenses for organizations that are looking to prioritize their defenses around actual adversary behavior. Focusing our energies on developing a set of common emulation plans that are available to all means that organizations can use their limited time and resources to focus on understanding how their defenses actually fare against real-world threats.
Why Use Adversary Emulation Plans?
Adversary Emulation mimics the behavior of real world threat actors in a safe and repeatable manner. Executing adversary emulation in your environment helps you answer questions such as:
- How do we build a resilient defense that is not based on static (and easily evaded) IOCs?
- How well do we detect, mitigate, respond to, or prevent against threat actor X?
- Are we collecting the right data and running the right queries to detect technique Y?
- How do we build the experience and skills on our team to defend against real-world threats?
- How do we tune our tools and processes to maximize efficacy against real-world threats?
Adversary Emulation Plans
The library contains two types of adversary emulation plans: full emulation and micro emulation.
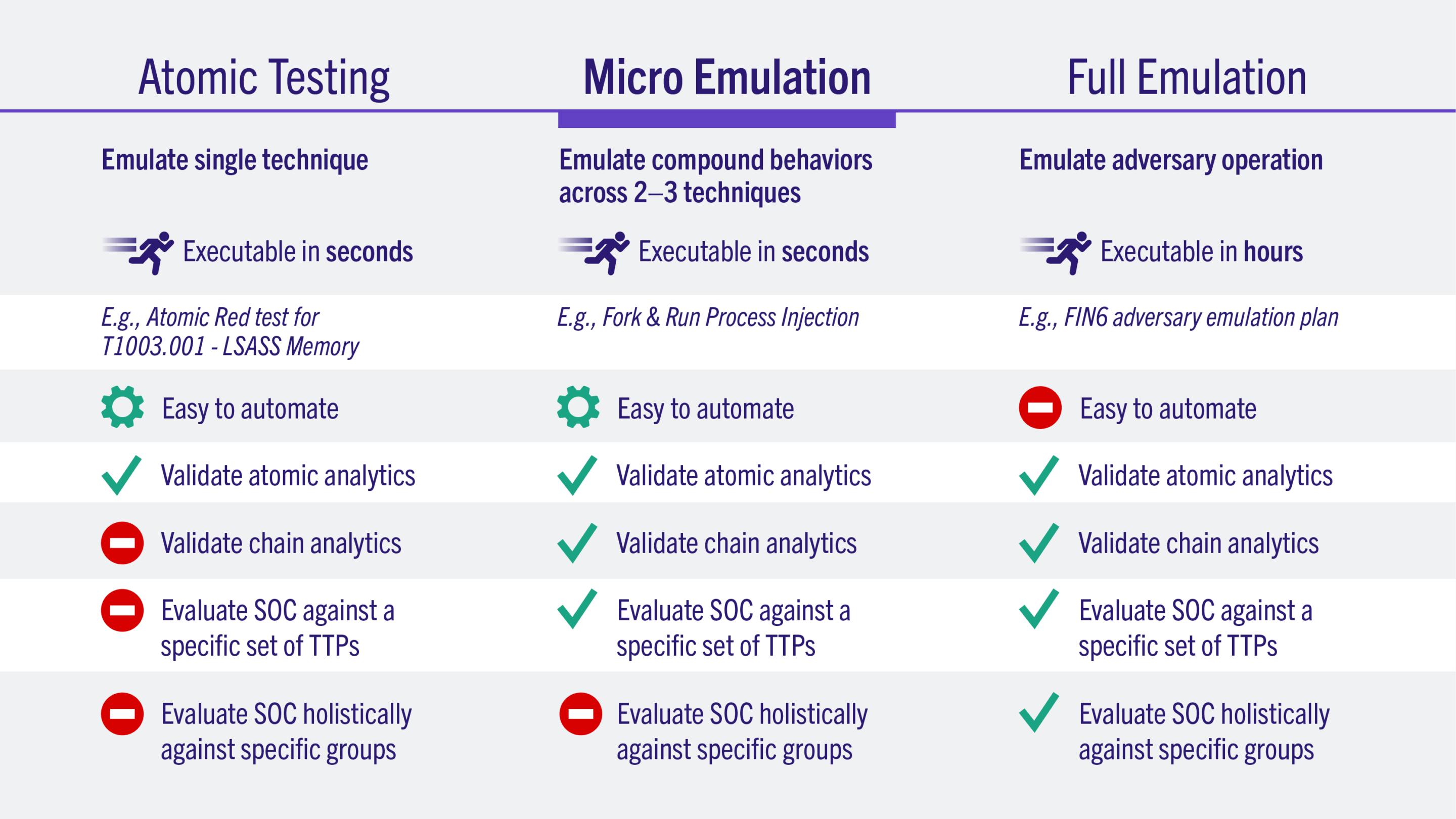
Full Emulation Plans
A comprehensive approach to emulating a specific adversary, e.g. FIN6, from initial access to exfiltration. These plans emulate a wide range of ATT&CK tactics & techniques and are designed to emulate a real breach from the designated adversary.
APT29
APT29 is thought to be an organized and well-resourced cyber threat actor whose collection objectives appear to align with the interests of the Russian Federation. The group is reported to have been …
Learn MoreBlind Eagle
Blind Eagle is a suspected South American threat actor that has been active since at least 2018. Targets are typically Colombian government institutions, as well as entities in the financial, …
Learn MoreCarbanak
Not to be confused with FIN7, Carbanak is a threat group that has been active since at least 2013. Using malware that shares its name, Carbanak has been known to target financial institutions, as well …
Learn MoreFIN6
FIN6 is a cyber crime group that has stolen payment card data and sold it for profit on underground marketplaces. Seen as early as 2015, this group has aggressively targeted and compromised point of …
Learn MoreFIN7
Not be confused with the Carbanak Group, FIN7 is a financially motivated threat group that has primarily targeted the U.S. retail, restaurant, and hospitality sectors since 2013. FIN7 traditionally …
Learn MoremenuPass
menuPass is thought to be motivated by collection objectives that align with Chinese national interests. menuPass has targeted healthcare, defense, energy, within Japan and USA.
Learn MoreOceanLotus
OceanLotus is a cyber threat actor aligning to the interests of the Vietnamese government. First seen in 2012, OceanLotus targets private corporations in the manufacturing, consumer product, and …
Learn MoreOilRig
OilRig is a cyber threat actor with operations aligning to the strategic objectives of the Iranian government. OilRig has been operational since at least 2014 with operations directed against …
Learn MoreSandworm
Responsible for the Ukranian power outage of 2017, Sandworm is a destructive threat group attributed to Russia's General Staff of the Armed Forces, Main Intelligence Directorate (GRU). Sandworm is …
Learn MoreTurla
Active since at least the early 2000s, Turla is a sophisticated Russian-based threat group that has infected victims in more than 50 countries.1 The group has targeted government agencies, diplomatic …
Learn MoreWizard Spider
Wizard Spider is a Russia-based e-crime group originally known for the Trickbot banking malware. In August 2018, Wizard Spider added capabilities to their Trickbot software enabling the deployment of …
Learn More
Micro Emulation Plans
A focused approach to emulating compound behaviors seen across multiple adversaries, e.g. webshells. These plans emulate a small amount of ATT&CK techniques that are typically performed as part of one adversary action
Active Directory Enumeration
Active Directory Enumeration emulates multiple Discovery behaviors through commonly abused interfaces and services such as Active Directory (AD).
Learn MoreData Exfiltration
Data Exfiltration emulates the compound behaviors of an adversary finding, staging, archiving, and extracting sensitive files.
Learn MoreDLL Side-loading
DLL Side-loading emulates an adversary executing an otherwise legitimate/benign application in order to hijack its modules/libraries to instead inject their malicious payload.
Learn MoreFile Access and File Modification
File Access and File Modification emulates file access and modification behaviors commonly associated with Collection as well as Data Encrypted for Impact.
Learn MoreLog Clearing
This micro emulation plan targets malicious activity associated with clearing Windows Event Logs. Adversaries and malware often target clearing and/or disabling the native logging provided by Windows …
Learn MoreNamed Pipes
Named pipes are shared memory used for inter-process communication (IPC). Named pipes are commonly abused by malware (ex: Cobalt Strike) while injecting/retrieving payloads and commands.
Learn MoreProcess Injection
Process Injection emulates the compound behavior of Process Injection followed by execution of arbitrary commands.
Learn MoreReflective Loading
Reflective Loading emulates an adversary running malicious code within an arbitrary process to perform Reflective Code Loading.
Learn MoreRemote Code Execution
Remote Code Execution emulates an adversary performing remote code execution against a vulnerable web server as documented.
Learn MoreUser Execution
User Execution emulates the compound behavior of delivering a malicious .one, .doc, .lnk, or .iso file (e.g. via Spearphishing Attachment) and then executing arbitrary commands after a user invokes …
Learn MoreWeb Shells
Web Shells emulates the compound behavior of planting a web shell and then executing arbitrary commands through it.
Learn MoreWindows Registry
Windows Registry emulates a few common methods that adversaries use to modify the Windows Registry.
Learn More


