Ambiguous Techniques
With Ambiguous Techniques, you will reduce false positives, focus on the highest‑value log sources, and uncover adversarial use of …
January 4, 2025
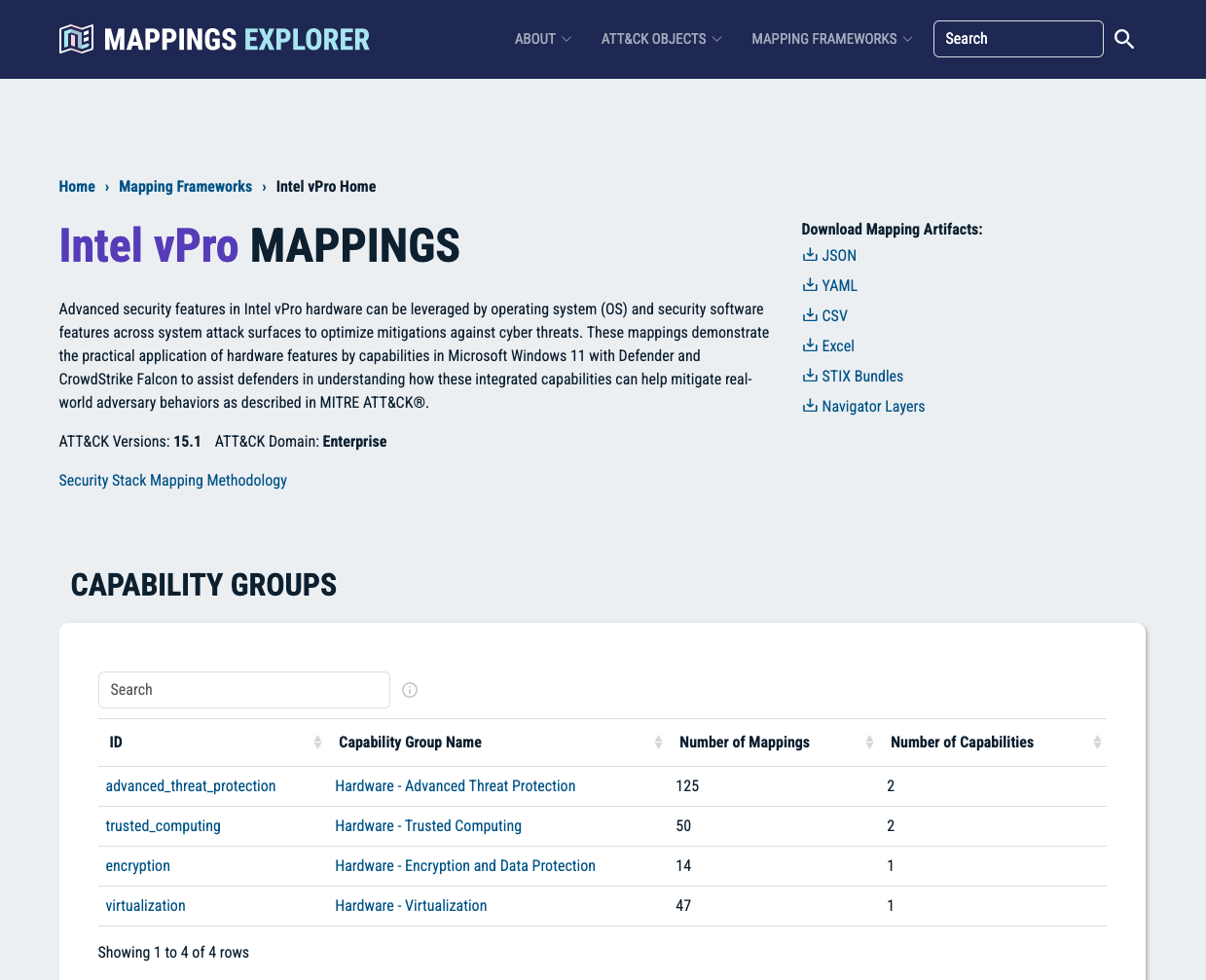
The Security Stack Mappings – Hardware-Enabled Defense project demonstrates full stack threat-informed defense, from the hardware board to the software bytes.
The Hardware-Enabled Defense mappings are part of our Mappings Explorer program. Use the Mappings Explorer website to navigate, explore, search, and download our mappings of security capabilities to MITRE ATT&CK®.
System security is available at the hardware level to provide protection from adversarial threats; however, these countermeasures are not well known to security practitioners.
Apply the security stack mapping methodology to connect hardware security capabilities of standard enterprise-class systems to adversarial behaviors as described in MITRE ATT&CK®.
Cyber defenders apply hardware-assisted security features to counter specific adversarial threats and provide defense-in-depth of systems and data, better securing billions of devices.




With Ambiguous Techniques, you will reduce false positives, focus on the highest‑value log sources, and uncover adversarial use of …
Use our latest mappings to replace assumption-driven cloud defense with evidence-based decisions to stop cloud adversaries in their tracks. With …
MITRE INFORM is a program-level assessment designed to show how threat-informed your organization is and where to improve next across cyber …
Sign up for our "Stay Informed" mailing list to receive announcements for project publications, upcoming events, and other news about the Center.