Secure AI
A collaboration with MITRE ATLAS™ to advance security for AI–enabled systems that takes a threat-informed approach, enables rapid exchange of new …
October 21, 2021
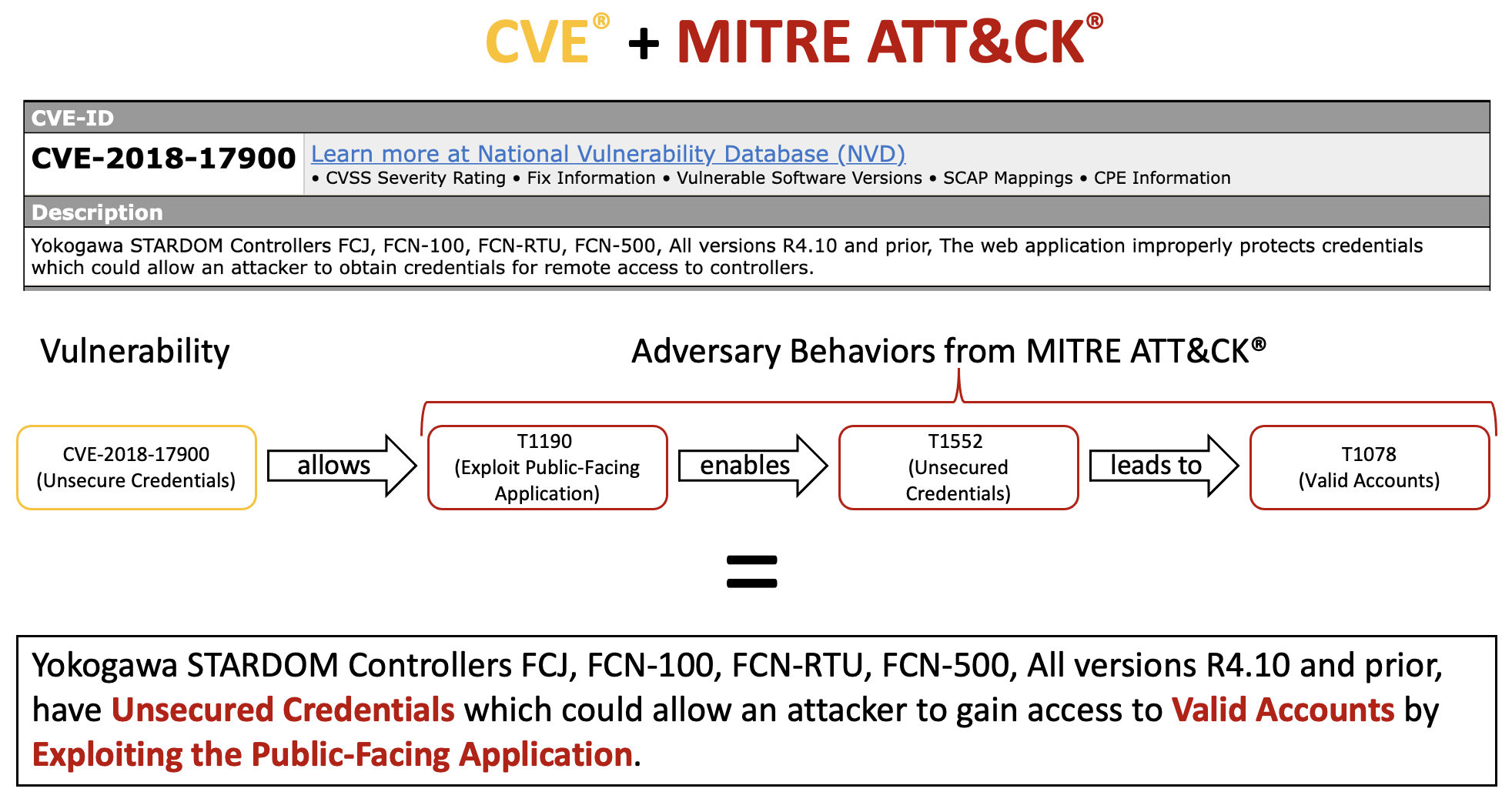
This research defines a methodology for using MITRE ATT&CK® to characterize the potential impacts of vulnerabilities. ATT&CK’s tactics and techniques enable defenders to quickly understand how a vulnerability can impact them. Vulnerability reporters and researchers use the methodology to describe the impact of vulnerabilities, enabling defenders to easily integrate vulnerability information into their risk models and identify appropriate compensating security controls. This methodology aims to establish a critical connection between vulnerability management, threat modeling, and compensating controls.
The CVE mappings are part of our Mappings Explorer program. Use the Mappings Explorer website to navigate, explore, search, and download our mappings of security capabilities to MITRE ATT&CK®.
Defenders struggle to integrate vulnerability and threat information and lack a consistent view of how adversaries use vulnerabilities to achieve their goals. Without this context, it is difficult to appropriately prioritize vulnerabilities.
Develop a methodology to use the adversary behaviors described in ATT&CK to characterize the impact of CVEs, providing much-needed context.
CVEs linked to ATT&CK techniques form a crucial contextual bridge between vulnerability management, threat modeling, and compensating controls, empowering defenders to better assess the true risk posed by specific vulnerabilities in their environment.


A collaboration with MITRE ATLAS™ to advance security for AI–enabled systems that takes a threat-informed approach, enables rapid exchange of new …
The Fight Fraud Framework strengthens fraud analysis by giving teams a clear behavioral structure to identify risks, focus investigations, and …
With Ambiguous Techniques, you will reduce false positives, focus on the highest‑value log sources, and uncover adversarial use of …
Sign up for our "Stay Informed" mailing list to receive announcements for project publications, upcoming events, and other news about the Center.