Fight Financial Fraud
The Fight Fraud Framework strengthens fraud analysis by giving teams a clear behavioral structure to identify risks, focus investigations, and …
July 8, 2025
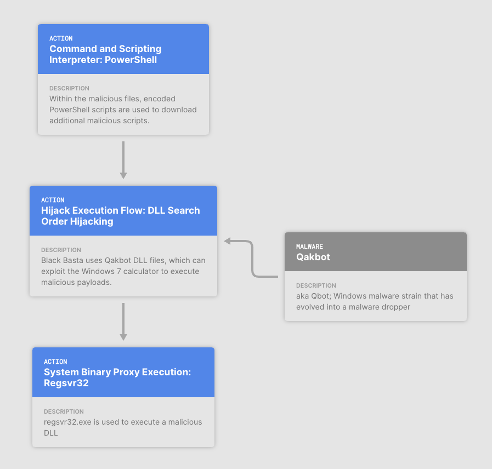
With Attack Flow, you will capture the entire attack and communicate what matters!
Tracking adversary behaviors one action at a time makes it hard to build effective defenses against multi-phased attacks.
Create a language, and associated tooling, to describe flows of ATT&CK techniques and combine those flows into patterns of behavior.
Visualize and communicate how adversaries operate to define defensive actions.






The Fight Fraud Framework strengthens fraud analysis by giving teams a clear behavioral structure to identify risks, focus investigations, and …
With Ambiguous Techniques, you will reduce false positives, focus on the highest‑value log sources, and uncover adversarial use of …
Use our latest mappings to replace assumption-driven cloud defense with evidence-based decisions to stop cloud adversaries in their tracks. With …
Sign up for our "Stay Informed" mailing list to receive announcements for project publications, upcoming events, and other news about the Center.