Ambiguous Techniques
With Ambiguous Techniques, you will reduce false positives, focus on the highest‑value log sources, and uncover adversarial use of …
February 17, 2026
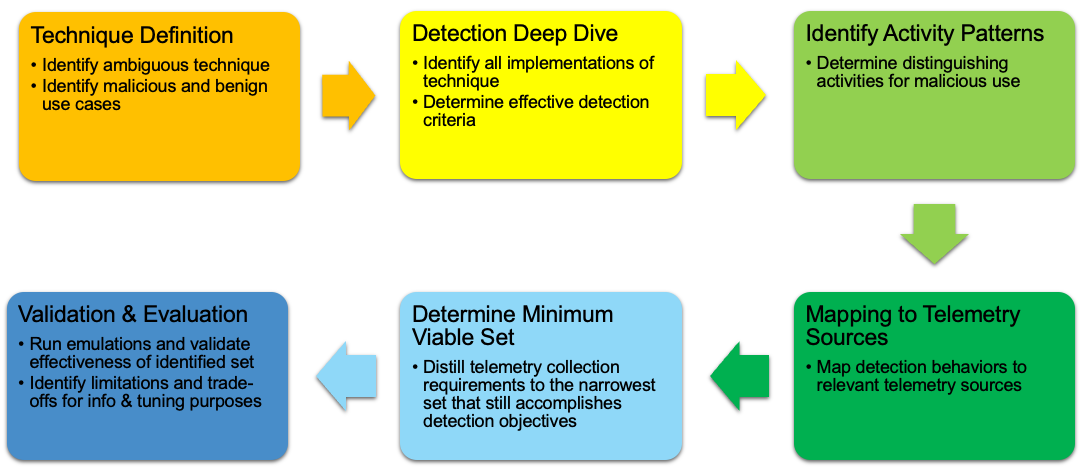
With Ambiguous Techniques, you will reduce false positives, focus on the highest‑value log sources, and uncover adversarial use of living‑off‑the‑land activity with an evidence‑driven detection design process.
Many ATT&CK techniques, especially those used in living-off-the-land activity, produce observables that are indistinguishable from benign behavior, making it difficult for defenders to determine malicious intent.
Apply contextual analysis, minimum telemetry requirements, and confidence‑based scoring of log sources to prioritize the data that most effectively separates malicious from benign use of ambiguous techniques.
Reduce false positives and improve detection accuracy so defenders can focus on the alerts that truly matter while using an evidence‑based approach to select and justify telemetry investments.







With Ambiguous Techniques, you will reduce false positives, focus on the highest‑value log sources, and uncover adversarial use of …
Use our latest mappings to replace assumption-driven cloud defense with evidence-based decisions to stop cloud adversaries in their tracks. With …
MITRE INFORM is a program-level assessment designed to show how threat-informed your organization is and where to improve next across cyber …
Sign up for our "Stay Informed" mailing list to receive announcements for project publications, upcoming events, and other news about the Center.